spica
Access control
Access control is a solution for managing the flow of employee and guest traffic through pre-defined entry points to aid in identification and security efforts. With access control software, you can monitor door status, track who is coming and going, and enable easy lockdown campus-wide, if necessary.
The goal of access control is to minimize the risk of unauthorized access to physical and logical systems. Access control is a fundamental component of security compliance programs that ensures security technology and access control policies are in place to protect confidential information, such as customer data.
The access control system is an electronic system which utilises electronic keys (the tags) to release door locks. The tag, which can be carried by the user on their key ring, is presented in the Proximity of a reader, located adjacent to a door and communicates with that reader utilizing encoded radio waves.
Spica Time & Space
![]()
Access control is the underlying function built into every Time&Space system. It deals with data about users, badges, access points and access rights. It also manages physically connected devices, handles alarms and collects event logs. All this provides the application framework for accommodating other higher level and add-on software modules, such as visitor management, video integration, working time clocking and time & attendance management.
Live control
Access control functionality is based on maintaining structured access profiles with programmed rules about who may enter, where and when. During normal operation, this information is automatically distributed to access controllers which are then capable of performing access control autonomously. In case of a communication dropout this will assure uninterrupted operation.
Once the communication is restored, all accumulated event logs will be automatically transferred to the system. During the normal online operation, doors can be controlled live directly from the software.
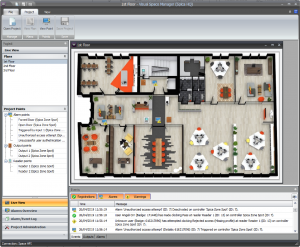
Visual monitoring
All access events, such as granted and rejected access, alarms and other signals are gathered by the system and shown in realtime. Live monitoring view provides spatial awareness by showing animated events popping-up on a floor plan.

Alarm management
The system provides powerful alarm management platform with user definable alarm categories, priority levels and automatic alarm handling workflow.
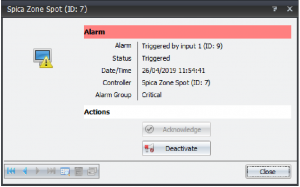
Realtime notification
Alarms and other events can be redirected to external recipients using various realtime notification methods, such as mail or text.
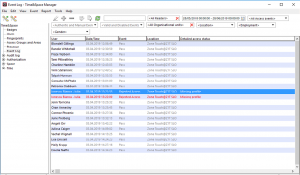
Event log
Event log is organized by various criteria and allows quick and deep forensic searches.
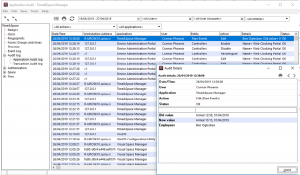
Audit log
Audit log option can be used as the ultimate solution for data integrity challenges. It is often required for larger systems because of higher security demands or privacy protection standards.
Some of other advanced features:
- Local Anti-Pass-Back
- Token based Global Anti-Pass Back
- Toggle access mode
- Two-man rule
- Elevator control
- Template-on-card
- Main Features
- Live control
- Visual monitoring
- Alarm management
- Realtime notification
- Event log
- Audit log
